We all have heard terms like “computer virus”, “worms”, etc. but little do we know their exact purpose and how these negatively affect our computer system. Most end users simply understand that their system is vulnerable and they need a fix by using some popular anti-virus software applications. What kind of threat they might be having or what kind of anti-virus software is suitable to most are the common issues people deal with. Before knowing how an anti-virus works, one must first know the types of malicious software that could be a potential threat to the computer system or an entire network as a whole.
1. Virus – Everyone is familiar with this term. This particular malware copies itself and is capable of spreading across the computers. They attach themselves to different programs and get executed if a user manually launches infected program. Viruses can spread via documents, script files, and cross-site scripting vulnerabilities in web apps.
2. Adware – Adware is an abbreviated form of advertising-supported software. It is not uncommon to witness its activities since the advertisements are everywhere in the form of pop-ups on the website. One also witnesses these pop-ups after the visit as these may appear on the browser. Not all Ads are potential threats but the chances of risks increase if someone blindly relies on the “free” versions of certain application software products that might be loaded with spyware as well.
3. Spyware – Spyware, as the name suggests, spies on the end-users’ activities without them being aware. They can monitor through keystrokes (saving the keypress event of users through a specific software and using it for personal gain), data harvesting (retrieving users’ account information, login details, etc.), and much more. Spyware can also modify the existing software’ or browser’s security settings, which results into interfering with network connections. If an existing software is vulnerable, it is easy for spyware to invade it.
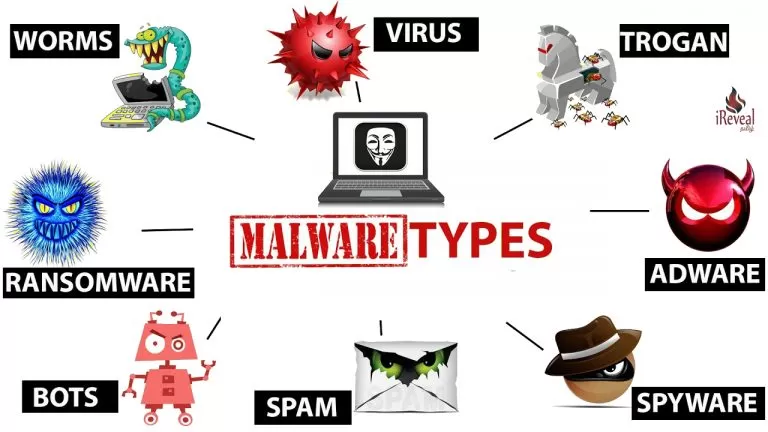
4. Ransomware – It is one of the most damaging threat one could get. This makes a computer system captive until the user pays money, usually in bitcoins. It restricts by encrypting the files on the hard drive, or by locking the entire system, displaying the message. It can travel through the network that might seem like a normal computer worm.
5. Worm – The worms spread among computers in a network usually cause harm to the host by consuming their bandwidth and unnecessarily overloading the web servers. Unlike a virus that needs human activity such as opening a file, running a program, etc. to spread itself, worms are independent of that and therefore can self-replicate without manual interference. In general, worms spread through sending mass emails across the network with infected attachments. This is why a responsible user must not open literally each kind of file that is sent by somebody unknown.
6. Trojan Horse – It appears a normal file to most users and so most people get tricked into downloading it. It then makes the computer vulnerable to unauthorized access and therefore the attacker can steal the end user’s data (like login details, financial information, electronic money, and so on), modify the existing files, monitor the user activities (using keylogging, screen watching, etc.), use the computer in botnets, and even install more malware!
7. Rootkit – Rootkit is a type of malware that is designed to gain access and control a computer system without getting detected by the security programs. Once it is installed, the attacker can execute the files, steal the sensitive information, and modify the system configurations. It is capable to even edit the security software! It can smartly hide its presence and so is difficult to get detected, prevented, and removing it.
8. Bug – Most programmers are familiar with this term. It is just an error that does not allow a small program or an application to run smoothly. If a bug is a major one, it can cause a system crash. The most severe among them all is the security bugs that can bypass user authentication, steal the data, or override access privileges. It could be prevented using code analysis tools and quality control, along with a hands-on knowledge of coding that deals with such kinds of issues.
9. Bot – Bots are designed to automatically perform various tasks. The most familiar bots belong to the search engines that crawl through the websites and list them as per the SEO norms. But it is possible (and quite common these days) that bots are used in botnets, that are basically collections of computers being controlled by the third parties. These could be prevented using CAPTCHA (“I am not a robot”) tests, that most authentic sites perform these days.
One may not be familiar with the security threats that might invade a computer system or an overall intranet of an organization. So, before it’s too late one must take note of the sure signs of malicious software’s presence.
1. Frequent freezing or system/application crash
2. Modified or absence of files
3. Difficulty in connecting to the networks
4. Intense CPU usage
5. Slow computer and/or web browser.
6. Strange files/plugins on the desktop or elsewhere that you haven’t downloaded
7. Emails being sent automatically to your contact list (by You!) without your knowledge
8. Strange computer’s behavior
9. Programs reconfiguring themselves and anti-virus and firewalls being turned off
If an organization wants to protect itself from any kind of malware, it needs to detect the vulnerabilities by itself, even before a malware does. Apart from detecting the vulnerabilities in the system software and the application software, the organization should avoid suspicious downloads. These steps should be taken by an expert team before using a genuine anti-malware software. This is because all software products are not one hundred percent perfect to detect all kinds of threat and therefore may even falsely detect a file which is not even a threat. Also, the anti-malware programs being used should be latest and well updated with the “latest threats”, so that these could see through the trouble.