Nmap is a shortform for Network Mapper. It is an open source security tool for network check, security scanning and auditing.
nmap command comes with a lots of options that make the utility more robust and difficult to follow for new users.
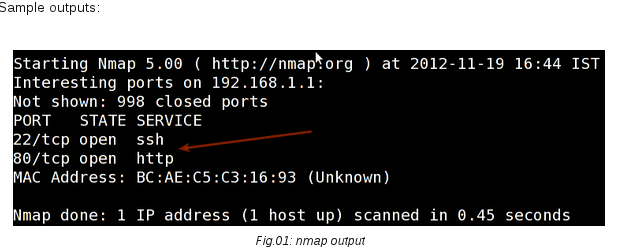
Scan an IP address (IPv4)
## Scan a single ip address ### nmap 192.168.1.1 ## Scan a host name ### nmap server1.example.com ## Scan a host name with more info### nmap -v server1.example.com
Scan multiple IPs address or subnet (IPv4)
nmap 192.168.1.1 192.168.1.2 192.168.1.3 ## works with same subnet as well i.e. 192.168.1.0/24 nmap 192.168.1.1,2,3
You can scan a range of IP address too:
nmap 192.168.1.1-10
You can scan a range of IP address using a wildcard:
nmap 192.168.1.*
Finally, you scan an entire subnet:
nmap 192.168.1.0/24
Read list of hosts/networks from a file (IPv4)
The -iL option allows you to read the list of target systems using a text file. This is useful to scan a large number of hosts/networks. Create a text file as follows:
cat > /tmp/test-file.txt
Sample outputs:
server1.example.com 192.168.1.0/24 192.168.1.1/24 10.1.2.3 localhost
The syntax is:
nmap -iL /tmp/test-file.txt
Excluding hosts/networks (IPv4)
When scanning a large number of hosts/networks you can exclude hosts from a scan:
nmap 192.168.1.0/24 –exclude 192.168.1.5 nmap 192.168.1.0/24 –exclude 192.168.1.5,192.168.1.254
OR exclude list from a file called /tmp/exclude.txt
nmap -iL /tmp/scanlist.txt --excludefile /tmp/exclude.txt
Turn on OS and version detection scanning script (IPv4)
nmap -A 192.168.1.254 nmap -v -A 192.168.1.1 nmap -A -iL /tmp/scanlist.txt